New York State SHIELD (Stop Hacks and Improve Electronic Data Security) ACT
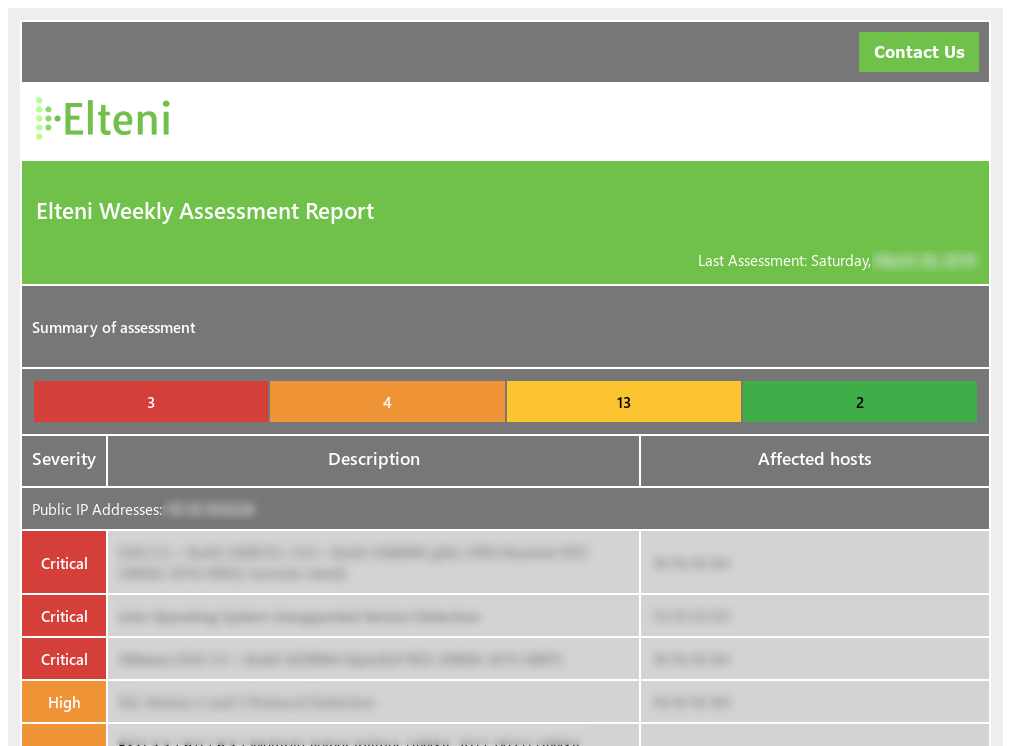
New York State SHIELD (Stop Hacks and Improve Electronic Data Security) will go into Effect March 21, 2020. This gives businesses a little less than nine months to become familiar with it and prepare for it entails. What is the SHIELD Act? The Stop Hacks and Improve Electronic Data Security (SHIELD) Act redefines data security