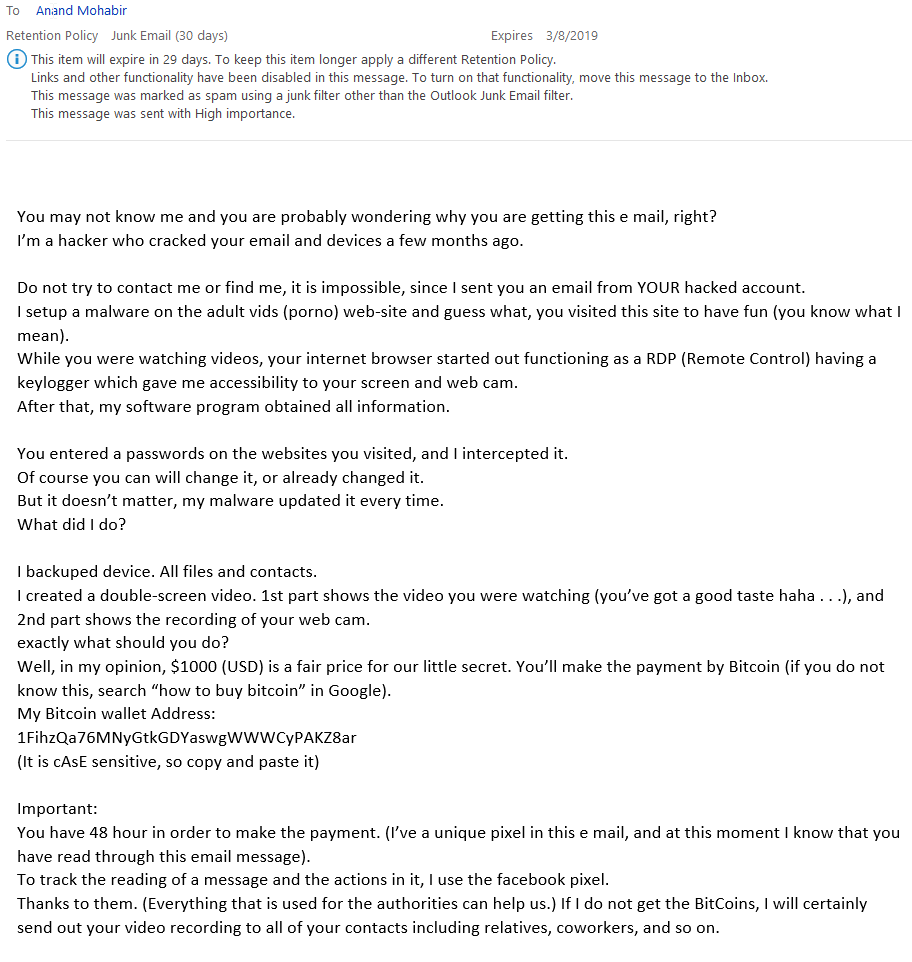
We got an email today that we thought was very interesting. Most of the email phishing campaigns that we’ve seen thus far, and the most common ones our clients typically get fall into two buckets: click a link or open an attachment.
We all know how effective some of these campaigns are. Lots of people fall victim to them, so they have proved to be very useful over time.
Today we got an email that made us laugh, but had our hearts beating a tad-bit faster (we’re totally innocent by the way). The reason for this is although the grammar is bad (to be expected) the email made us think. The sender attempted to use scare tactics to invoke fear, curiosity, and had us questioning the truth. Crazy, huh?!
Forget about this sender trying to compromise a computer, encrypting data and then asking us to pay bitcoin for the data. They went straight to telling us we need to pay bitcoin because they have some sensitive information about us, and if we didn’t pay all of our friends and family and co-workers would get the video of us (not sure how they got a video, we use webcam covers :o). (If you need one, reach out and we’ll send you one with our nifty logo).
Something to note is they spoofed the sender email address to make it look like my own. Dead give away that this is a typical phishing technique being used when you look at the sender email address. If you wanted to dig deeper, analyze the headers and you can clearly see it is coming from a suspicious location.
We felt the need to share this email so you share in our experience, get a chuckle, but also be aware of the easier techniques being used to try and extort money from you.